The drone threat continues to evolve—both on the battlefield and now in the homeland—making it critical for counter-UAS (C-UAS) technology to always be a step ahead of the enemy.

Countering nefarious drones is what many describe as a never ending game of cat and mouse. A threat is identified, a defense is deployed, the threat evolves to overcome that defense, and another defense must be fielded. The fact drones have become more sophisticated yet less expensive is accelerating that cycle, giving adversaries more opportunities to break through counter-UAS (C-UAS) protections.
We’re seeing that play out in Ukraine and other conflicts, serving as a stark reminder that thwarting today’s threat isn’t enough; we must be prepared for what’s coming tomorrow. Take first person view (FPV) drones as an example. Initially, these drones were guided by a radio frequency (RF) signal that had to be constantly maintained, said Adam Robertson, Fortem Technologies co-founder and CTO. The signal could be detected, the operator located and hostile drones taken over via jamming. Adversaries are now flying “dark drones” over fiber optics that can’t be detected or jammed, changing the game.
“Because drones are using a fiber optic cable to maneuver to the target, they now have to use different types of sensors, a whole litany of sensors, to triangulate and defeat or disable that drone,” said Daniel Dross, Silvus Technologies director of sales, Army & C-UAS. “And they’re proliferating throughout the battlefield.”
To keep up with this rapidly changing threat, long military procurement and research times are not sustainable, said Dane Pigott, CEO of Kinard Technologies. C-UAS solutions must be deployed at scale to protect our soldiers. He expects to see more of that in 2026, with the Department of Defense (DoD) signaling it’s “starting to prioritize fielding more than research.”
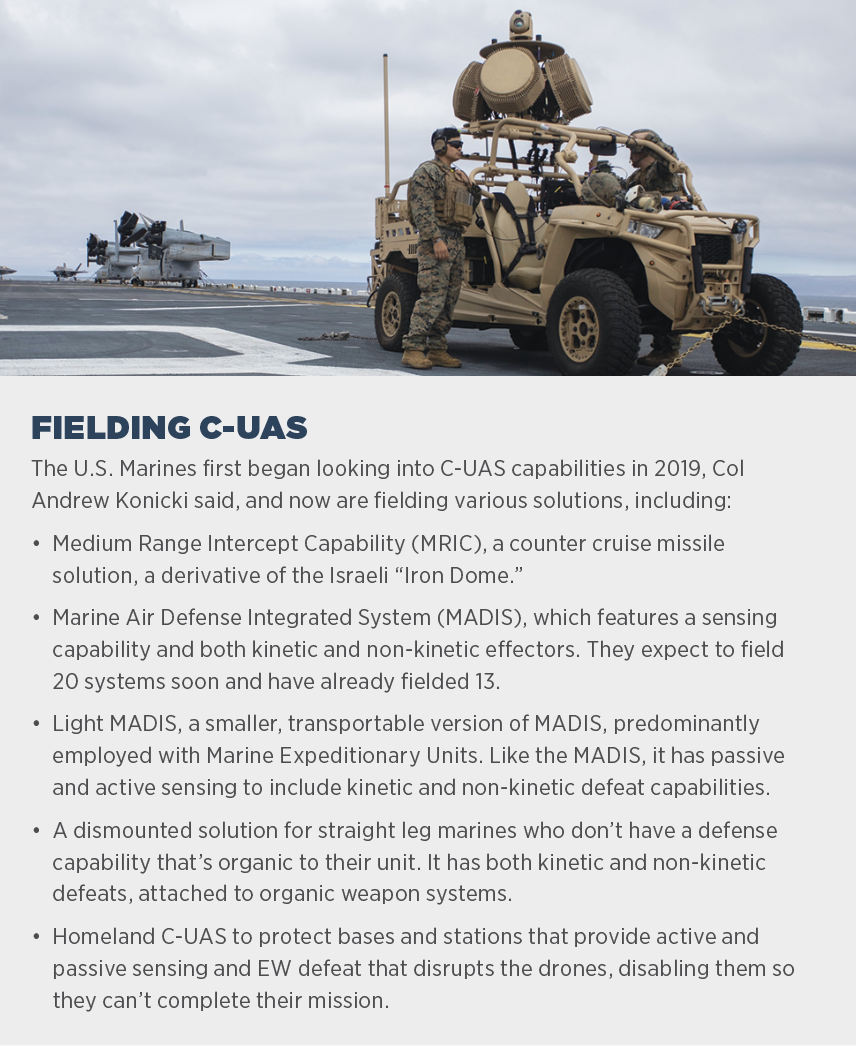
And there has been movement. The U.S. Marines, for example, is fielding or preparing to field several C-UAS technologies. They’re constantly monitoring the threat through intelligence sources to adapt and iterate current capabilities, Program Manager for Ground Based Air Defense Col Andrew Konicki said. User feedback from soldiers in the field also plays a critical role.
“If we waited for the perfect solution we would never field,” he said. “We get it out there and iteratively improve on the capability to keep pace with the threat.”
Countering hostile drones isn’t just a problem for the military; it’s an issue in the homeland, too. UAS pose threats to critical infrastructure, large public gatherings, correctional facilities, airports, U.S. borders and military bases, to name a few vulnerabilities. The “battlefield can be anywhere,” said Leo McCloskey, Echodyne vice president of marketing, meaning C-UAS solutions must be flexible, multi layered, and adaptable to any threat no matter where it is.
“The need to do this is now,” Robertson said. “We can’t study this to death. We need solutions, even if it’s a 90% solution, get it out there. Have it installed before it’s too late. Ninety percent is better than 0%.”

FINDING THE THREAT
Protecting against hostile drones starts with detect, identify and track. Radio frequency has been the most common way to accomplish that, with Dedrone by Axon developing a radio signature library that can detect about 500 drone models and 100 manufacturers, said Travis Scott, vice president of commercial sales. That library continues to evolve as more drones enter the space and serves as the “foundation” of a multi-layered approach.
Wide view cameras, acoustics and radars have also emerged as critical pieces, especially as enemies find ways to eliminate the RF signal. Radar has proven effective in detecting hostile drones, Robertson said, as it can scan a wide area and look for small objects in the air. Cameras are leveraged for image recognition and identification.
Radar is an active sensor, though, which makes it a target, McCloskey said. Echodyne’s radar features flash on and flash off to overcome this. As part of a layered system, other sensors like acoustic panels can trigger the radar’s flash on to obtain the data needed to move to the next layer, and then flash off again.
When possible, passive techniques that look for emissions off platforms can help identify threats earlier, said Stu Wildman, Senior VP of Programs, Mission Systems & Technology at SNC. Active techniques can then be deployed to track, engage and confuse the drones. Taking the drone out early is the best approach.
“You want to cast as wide a net as possible for detection,” he said, “and then use layers in that net to decide how you want to address it.”
Regardless of the method used, C-UAS must consistently determine what’s a bird and what’s a drone, and which drones are friends and which are foes. That’s where AI is playing a critical role. It’s no longer seen as a nice to have classification, DroneShield Product Intelligence Analyst Agostino Manfre said. It’s now part of the core decision loop.

“When you put data streams together in a rapid fashion with high accuracy, it all contributes to the data puzzle,” McCloskey said. “Then you can apply AI, and that gets you speed of relevance and response. One of the most important things is how fast you can move. These things can be coming at you at 45 mph, so you don’t have a lot of time to respond.”
With help from AI, radars and other sensors feed data into command and control (C2), another key element of a C-UAS solution, which then makes identification and recommendations for the operator, said Bob Kelley, senior director in Land & Air Defense Systems at Raytheon, an RTX business. This helps take the burden off operators, who, along with the sensor systems, are being “overwhelmed” with mass drone raids, one of the latest evolving threats.
AI can make drone swarms easier to detect and deal with by identifying the most important threats to eliminate, Wildman said. Swift action can then be taken against drones moving toward high value targets.
“One attribute we’re looking to improve on is automatic target recognition using AI because of cognitive overload and the increasing swarm threat,” Col Konicki said. “When you have so many things flying in the air, you need sensing capability. We can use AI to detect what is a threat and what isn’t, and eliminate false positives so we can focus on the real threat and use whatever kinetic and non-kinetic means available to us to defeat it.”
Of course, one size doesn’t fit all, said Greg Fortier, Senior VP, Army Business Group for SAIC. SAIC’s software takes a modular, open system approach that makes it possible to add any sensor needed for the mission set, keeping the “ecosystem of sensors and effectors aligned appropriately.” It is integrated with more than 60 sensors, can operate with any legacy or future network and be tailored to specific mission sets.
Col Konicki describes the threat these C-UAS technologies are addressing as “highly prolific and indiscriminate.”
“At first, everything was DJI drones and RF disruption to counter the signal,” he said. “Where we’re seeing change is high power, microwave lasers, and other non-kinetic means of disrupting the signal, how drones are controlled and their speed. As drones evolve, we have to maintain that pace or our folks are put at risk.”
MITIGATION ON THE BATTLEFIELD
Various C-UAS sensors are available on the detection side, leveraging AI to detect hostile drone threats and quickly relay that information back to operators, said Justin MacLaurin, President and CEO of Digital Force Technologies. Countermeasures are informed by the data captured, and operators must be able to trust it’s accurate every time.
There’s a range of kinetic and non-kinetic effects that can be deployed based on the size of the drone, where it is and the threat it poses. The most effective C-UAS solutions, Kelley said, integrate both, presenting multiple problems the enemy must deal with at once.
“C-UAS in defense has shifted from detect and jam a hobby drone to managing a full spectrum of threats: long-range one-way attack drones, FPV loitering munitions on low, fast profiles, and small quadcopters used for ISR, all operating in dense RF and kinetic environments,” Manfre said. “Modern systems are effective when they can correlate those threats across RF, radar, EO/IR and cooperative feeds, then cue the right effector, electronic or kinetic, fast enough to matter.”
The enemy is deploying more autonomous drones that can’t be detected, creating a new set of problems, said Scott Estes, Teledyne FLIR Defense Director for Army and Joint CBRNe Systems. Once targeted, they’ll likely require a “hard kill” with either kinetic effectors or directed energy like a laser or high power microwave.
Directed energy effectors, though, have limited range, are expensive and difficult to scale, Robertson said. Missiles work, but cost per shot is a concern, while machine guns and miniaturized weapon systems also have been leveraged.
Because existing weapon systems aren’t well equipped for mitigating enemy drones, there’s been a push to develop new kinetic systems, Pigott said.
For Kinard, that’s BAOWOLF, a large caliber FPV munition that makes it easy for soldiers to hit moving drone targets, Pigott said. Its AMPT solution, once plugged into detection networks, can slew to targets and automatically defeat them.
“Some engagements are just seconds. If you wait for a solider to slew, it’s already over,” Pigott said. “This is capable of full autonomy, but there is a man in the loop to ask for permission to engage.”
RTX’s C-UAS solution includes Ku-band Radio Frequency Sensor (KuRFS) radar, C2 and the Coyote effector, a low-cost, rail-launched missile variant. The radar is “exceptionally accurate” at detecting small, low flying threats like UAS, Kelley said, and, along with the c2 system, guides the Coyote to the threat. These capabilities are components of the U.S. Army’s deployed C-UAS solution, the Low, Slow, Small, Unmanned Aircraft Integrated Defeat System (LIDS).
On the non-kinetic side, EW techniques can disable drone threats, Wildman said, eliminating the collateral damage that comes with kinetic effectors.
Dedrone, which offers a handheld device that jams drone signals, is working with a partner to create a cyber solution that “tricks the drone into thinking you are the controller,” another increasingly popular mitigation option.
D-Fend Solutions combines AI and cyber to understand the drone’s brains and communication protocols, with the goal of near zero false alarms even in crowded airspace, Chief Marketing Officer Jeffrey Starr said. Quickly distinguishing between what’s friend and what’s foe and then choosing the mitigation that nets the least amount of collateral damage and operational disruption is “mission critical.” With D-Fend’s technology, pilots take control of the drone, land it safely and retrieve critical intelligence.
Drone inceptors, like Fortem’s DroneHunter, leverage on-board radar to look for a target, pursue it, capture it with a net and take it to a safe place for forensics analysis, Robertson said. Soldiers can look for weapons, including chemical and biological, and determine where it was sold and the data it collected.
Regardless of the mitigation leveraged, there must be a network in place to support the “interoperability of the hundreds, perhaps thousands” of sensors and effectors deployed in a given battlespace,” Estes said. Sensor data must be rapidly processed to identify the best and most cost effective effector to engage, and then alert it.
“That’s where we’re headed,” Estes said. “We’re seeing a greater awareness across all services and in the homeland of this idea, this need to pool the great capabilities we have and make them work more seamlessly—not just at a system level but across whatever area of operation you’re in.”
THE THREAT TO THE HOMELAND
As we saw with operation Spiderweb in June, when Ukraine smuggled drones deep into Russia, hostile drones could be “right next door,” ready to attack the homeland, McCloskey said, making large sporting events, military bases, parades, airports and critical infrastructure all vulnerable.
But you can’t manage these threats like you would on a battlefield, Starr said. Detection, identification and tracking are the same, but shooting a drone out of the sky or jamming it aren’t options.
“As the threat moves away from the battlefield, you need solutions that are more safe, surgical, smart and non-disruptive,” Starr said. “This evolution has created a set of different requirements that have in turn generated massive demand for new technology.”
As it stands, only a handful of federal agencies can take any action at all. If local law enforcement detects a rogue drone, for example, while they can gain vital information about the drone and its location, their only recourse to stop it from flying is to contact the pilot, a frustration for many. That’s expected to change soon, though.
The more defined threat has led to a push to enact legislation that enables local law enforcement and security forces to disable and destroy nefarious drones flying, say, over critical infrastructure, Pigott said.
“People are waking up to the threat,” he said. “We’ve seen more requests from the civilian side in the last three months than in the last three years.”
Already, C-UAS solutions are providing protection beyond the battlefield, protecting large events and critical infrastructure from attacks. SAIC, for example, has deployed C-UAS attheOlympics and the G8 Summit, Fortier said.
The 2026 FIFA World Cup has become a big area of focus. World Cup games will be played in 11 U.S. cities, with each having a chance to obtain a portion of the $500 million in grant funds allocated for C-UAS, Scott said. Each host city has a task force, made up of public safety agencies, focused on identifying C-UAS technology they’d like to deploy. Any city that completes the required training can submit for authorization to mitigate threats during the World Cup.
“That’s something that’s never been seen before at the local level,” Scott said, “and will be a catalyst that shows this can be done safely and effectively.”
LOOKING AHEAD
Drones are evolving quickly, and C-UAS technology must follow suit. It’s critical to not only understand today’s threat, Kelley said, but the technologies adversaries may leverage in future battlefields.
“As everybody has seen in Ukraine, the threat iterates very quickly,” said Ray Fitzgerald, Senior VP of Strategy, ISR, Aviation & Security business area for SNC, “and the ability to counter that in a layered defense system is very important.”
The constant evolution of C-UAS capabilities will be driven by the threat and user feedback, Col Konicki said, with no one solution able to provide all the necessary defensive measures.
“We need a layered approach that leverages everything from missiles to directed energy to bullets to non-kinetic means,” he said. “All those things have to be used in a package in conjunction with one another rather than in isolation.”
On the homeland side, the number of drones is only increasing, Starr said, and with that the number of incidents and vulnerable assets. Protection must move from small areas to vast domains, making it critical for the technology to be adaptable and updatable. And more users must be able to access it.
Instrumentation of the airspace will also prove critical, McCloskey said, to overcome the “needle in the haystack” problem of finding nefarious actors.
“Operation Spiderweb was 117 drones and that was considered large scale,” MacLaurin said. “Then you look at China doing light shows with 12,000 drones. It’s a simple programming difference to make that into a weapon. Consider 12,000 drones coming down on a population. …We have good assets and bad assets in the air, how do we discern between the two? It’s instrumentation of the airspace.”
Autonomous and semi-autonomous countermeasures have already matured into “edge devices that can classify, prioritize and propose or execute jamming profiles against swarms with minimal operator input while still keeping a human on the loop,” Manfre said. In the future, he expects C-UAS to “converge with broader air domain awareness” and to be managed as “part of a unified air picture with common command and control.”
There will be deeper uses of autonomy at the edge, he said, such as forward nodes that can detect, classify and recommend mitigation, and tighter integration with kinetic effectors and EW. There will also be more focus on FPV and swarm threats.
“A sensor agnostic, software-defined C-UAS layer must be added, he said, to “absorb new threat profiles and new effectors without rebuilding the architecture each time.”
C-UAS will become part of critical infrastructure protection, Wildman said, and that will involve scaling. The industrial base will have to provide quantities that are necessary today, next week and next year, and do so economically.
Each limited area of defense must talk to each other and tie into a bigger picture, creating a “golden dome” defending the homeland, Fitzgerald said. Solutions must have the ability to right size, Wildman said, and the acquisition process streamlined. Systems need to communicate, and, if there’s ever a coordinated attack, alert the right people.
Layered, adaptable solutions must be fielded quickly, as this threat isn’t going away.
“We are at a risk of attack by our enemies,” Robertson said, “unless we have something in place.”